Introduction
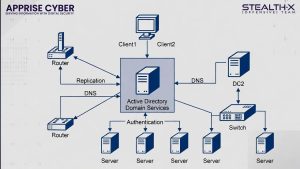
Active Directory (AD) is the backbone of identity and access management in most enterprise environments. It is responsible for authenticating users, managing permissions, controlling access to systems, and organizing network resources. Because of this central role, compromising Active Directory often means compromising the entire organization.
Cybersecurity researchers estimate that around 90% of modern cyberattacks involve Active Directory in some stage of the attack lifecycle. Once attackers gain even limited access to an AD environment, they can perform reconnaissance, steal credentials, escalate privileges, and move laterally across the network.
Attackers exploit weaknesses such as misconfigured permissions, weak passwords, legacy protocols, and poorly secured service accounts. Understanding the most common Active Directory attack techniques is essential for organizations that want to protect their infrastructure and prevent large-scale breaches.
In this article, we will explore the Top 10 Active Directory attacks, how they work, and why they are dangerous to enterprise networks.
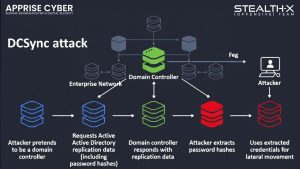
- DCSync Attack: Attackers abuse the directory replication process by pretending to be a domain controller to request replication data, including password hashes of all users.
- Golden Ticket Attack: Forging a Kerberos Ticket Granting Ticket (TGT) using the password hash of the krbtgt account. This allows attackers to impersonate any user and maintain domain admin privileges.
- BloodHound Reconnaissance: Using graph theory to analyze relationships and map trust paths between users, groups, and computers to find the shortest path to domain administrator.
- NTDS.dit Extraction: Copying the main Active Directory database file from domain controllers to perform offline credential dumping of all user accounts.
- Misconfigured Access Control Lists (ACLs): Improperly configured permissions that allow lower-privileged users to reset passwords, modify group memberships, or change object permissions.
- Unconstrained Delegation: A legacy configuration that allows a server to impersonate a user on any service in the domain, allowing attackers to capture privileged Kerberos tickets.
How Organizations Can Defend Against AD Attacks
| Defense Strategy | Implementation Measure |
|---|---|
| Tiered Administration | Separate admin accounts from regular user accounts. |
| Enforce MFA | Require multi-factor authentication for all privileged users. |
| Legacy Protocols | Disable insecure protocols like LLMNR, NBT-NS, and NTLM. |
| Managed Accounts | Implement Group Managed Service Accounts (gMSA). |
Secure Your Active Directory with Apprise Cyber
Active Directory remains one of the most targeted components in enterprise cyberattacks. Apprise Cyber provides specialized cybersecurity services including:
- Active Directory Security Assessments
- Penetration Testing
- Threat Detection & Monitoring
- Identity and Access Management Security
- Vulnerability Management
If you want to protect your organization from modern AD attacks, contact Apprise Cyber today and strengthen your cybersecurity posture.
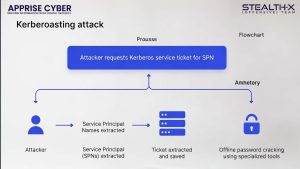
1. Kerberoasting Attack
Kerberoasting is one of the most widely used credential-theft techniques in Active Directory environments. It targets service accounts that use Service Principal Names (SPNs) for authentication through the Kerberos protocol. In a Kerberos authentication process, a user can request a Ticket Granting Service (TGS) ticket for a service associated with an SPN. This ticket is encrypted using the password hash of the service account.
Attackers first gain access to a normal domain user account.
They request TGS tickets for multiple services with SPNs.
These tickets are captured and exported.
The attacker performs offline brute-force cracking to retrieve the service account password.
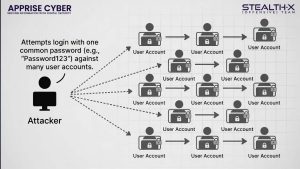
2. Password Spraying
Password spraying is a stealthy brute-force attack designed to bypass account lockout mechanisms. Traditional brute-force attacks attempt multiple passwords against a single account. This quickly triggers account lockouts and alerts. Password spraying takes a different approach.
Select one common password (for example, Welcome2025!).
Attempt that password across hundreds or thousands of user accounts
Because each account only receives one login attempt, lockout thresholds are rarely triggered. If even a single user account matches the password, the attacker gains valid credentials and can begin lateral movement across the network.
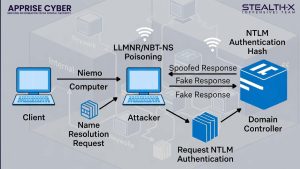
3. LLMNR / NBT-NS Poisoning
Link-Local Multicast Name Resolution (LLMNR) and NetBIOS Name Service (NBT-NS) are legacy Windows protocols used for hostname resolution when DNS fails. These protocols broadcast requests across the local network to find a machine’s IP address. Attackers exploit this mechanism by spoofing responses.
A victim machine broadcasts a request asking for a hostname.
The attacker’s system responds first, pretending to be the requested host.
The victim system attempts authentication with the attacker.
The attacker captures the NTLMv2 authentication hash.
4. Pass-the-Hash (PtH)
Pass-the-Hash is a credential abuse technique that allows attackers to authenticate without knowing the actual password. Instead of stealing plaintext passwords, attackers extract NTLM password hashes from system memory. Common tools used for this purpose include Mimikatz, Impacket, and CrackMapExec.
The attacker compromises a system.
Credential hashes are extracted from LSASS memory.
The attacker uses these hashes to authenticate to other systems.
5. DCSync Attack
DCSync is one of the most dangerous attacks targeting Active Directory replication mechanisms. Domain Controllers regularly replicate directory data between each other. Attackers abuse this process by pretending to be a domain controller and requesting replication data. If an attacker gains an account with replication privileges, they can request credential data from the domain controller including password hashes of all users, administrator credentials, and service account credentials.
6. Golden Ticket Attack
The Golden Ticket attack is considered one of the most powerful persistence techniques in Active Directory. This attack involves forging a Kerberos Ticket Granting Ticket (TGT) using the password hash of the krbtgt account, which is responsible for signing Kerberos tickets. If attackers obtain the krbtgt hash, they can generate fake authentication tickets to impersonate any user, grant themselves Domain Admin privileges, and maintain access for years.
7. BloodHound Reconnaissance
BloodHound is a powerful tool used to analyze relationships within Active Directory. Instead of directly attacking systems, BloodHound performs advanced reconnaissance by mapping trust relationships between users, groups, computers, and permissions. It uses graph theory to identify the shortest path from a low-privileged user to Domain Administrator, providing attackers with a complete attack roadmap.
8. NTDS.dit Extraction
The NTDS.dit file is the main Active Directory database stored on Domain Controllers. This file contains all user accounts, password hashes, and group memberships. If attackers obtain administrative access to a Domain Controller, they may attempt to copy the NTDS.dit file. Once extracted, attackers can perform offline credential dumping to retrieve all password hashes in the domain, effectively exposing the entire authentication infrastructure.
9. Misconfigured Access Control Lists (ACLs)
Access Control Lists (ACLs) define permissions on Active Directory objects such as users, groups, and organizational units. Improperly configured ACLs can allow lower-privileged users to reset passwords of other users, modify group memberships, or change permissions on objects. Attackers actively search for these misconfigurations because they allow privilege escalation without exploiting vulnerabilities.
10. Unconstrained Delegation
Delegation allows services to authenticate on behalf of users to access other services. Unconstrained delegation is a legacy configuration that allows a server to impersonate a user on any service in the domain. Attackers exploit this by forcing a Domain Controller or privileged user to authenticate to a compromised machine. When authentication occurs, the attacker can capture the user’s Kerberos ticket and reuse it to impersonate that user.