How Artificial Intelligence Is Redefining Cybercrime
Introduction
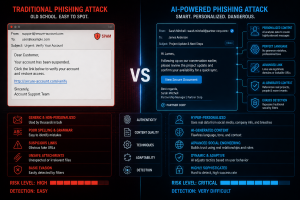
The digital world is rapidly evolving, and with every technological advancement comes a new wave of cybersecurity threats. Among the most alarming developments in recent years is the rise of AI-powered phishing attacks. Traditional phishing scams once relied on poorly written emails and obvious fake websites, making them relatively easy to identify. Today, however, cybercriminals are leveraging Artificial Intelligence (AI) to launch highly sophisticated phishing campaigns that are intelligent, automated, personalized, and extremely difficult to detect.
Artificial Intelligence has transformed industries worldwide by improving automation, decision-making, and efficiency. Unfortunately, attackers are also exploiting the same technologies to enhance cybercrime operations. AI-powered phishing attacks now have the ability to mimic human communication, analyze victim behavior, generate convincing content, and manipulate individuals with remarkable accuracy.
For businesses, governments, and individuals alike, this emerging threat represents a serious cybersecurity challenge that cannot be ignored.
Understanding Phishing Attacks
Phishing is a form of cyberattack in which attackers impersonate legitimate organizations, brands, or trusted individuals to trick victims into revealing sensitive information. This may include:
- Usernames and passwords
- Banking details
- Credit card information
- Company credentials
- Personal identification data
- Multi-factor authentication codes
Phishing attacks commonly occur through:
- Emails
- Fake websites
- SMS messages
- Social media platforms
- Voice calls
- Messaging applications
The primary objective is usually financial theft, unauthorized access, identity theft, or malware deployment.
While phishing has existed for decades, AI has dramatically increased both its effectiveness and scalability.
The Rise of AI in Cybercrime
Artificial Intelligence enables machines to simulate human intelligence processes such as learning, language generation, data analysis, and decision-making. Cybercriminals now use AI tools to automate and optimize phishing campaigns on a massive scale.
Instead of sending generic emails to random victims, attackers can now:
- Analyze personal data from online platforms
- Create personalized phishing messages
- Clone voices and generate fake videos
- Conduct automated conversations
- Adapt attack strategies in real time
This combination of automation and personalization has made modern phishing attacks significantly more dangerous than traditional methods.
How AI-Powered Phishing Attacks Work
- Data Collection and Victim Profiling
AI systems can gather information from multiple public sources, including:
- LinkedIn profiles
- Facebook accounts
- Corporate websites
- Online forums
- Social media posts
- Public databases
Attackers analyze this data to build detailed victim profiles containing:
- Job positions
- Company relationships
- Interests and hobbies
- Communication styles
- Recent activities
This information helps attackers create highly believable phishing messages tailored specifically to the victim.
For example, an employee may receive an email appearing to come from their manager referencing an actual ongoing project or recent company event.
- AI-Generated Phishing Emails
Modern AI language models can produce professional-quality emails that closely resemble legitimate business communication.
Unlike traditional phishing messages, AI-generated emails often contain:
- Proper grammar and spelling
- Natural language patterns
- Professional formatting
- Context-aware messaging
- Emotional manipulation techniques
These emails can imitate:
- CEOs
- HR departments
- Banks
- Cloud service providers
- Vendors
- Business partners
Because the messages appear authentic, victims are more likely to trust them and take immediate action.
- Deepfake Voice and Video Phishing
One of the most concerning advancements in AI-powered phishing is deepfake technology.
Deepfake systems use machine learning algorithms to create realistic fake audio and video content. Attackers can now clone voices or generate videos that mimic trusted individuals with shocking accuracy.
Examples include:
- A fake CEO voice requesting an urgent money transfer
- A fraudulent video meeting invitation
- AI-generated customer support representatives
- Fake executive approval calls
These attacks are particularly dangerous because people naturally trust familiar voices and faces.
Several real-world organizations have already suffered financial losses due to AI-generated voice phishing scams.
- AI Chatbot Social Engineering
Cybercriminals increasingly use AI-powered chatbots to engage with victims in real time.
These bots can:
- Pretend to be customer support agents
- Guide victims to fake login portals
- Ask for verification codes
- Respond naturally during conversations
- Adapt responses dynamically
Unlike basic scripted bots, AI chatbots can maintain convincing conversations that make scams appear legitimate.
- Automated Large-Scale Attacks
Artificial Intelligence allows attackers to launch phishing campaigns at an unprecedented scale.
Traditional spear-phishing attacks required manual effort and significant preparation. AI now automates much of the process, enabling attackers to target thousands of individuals simultaneously while maintaining personalization.
This scalability significantly increases the probability of successful attacks.
Why AI-Powered Phishing Is More Dangerous
Increased Realism
AI-generated messages closely resemble legitimate communication, reducing common warning signs that users typically rely on.
Advanced Personalization
Attackers can craft messages specifically tailored to each victim, increasing trust and engagement.
Faster Attack Deployment
AI automates content generation, victim targeting, and communication, enabling rapid attack execution.
Reduced Human Effort
Cybercriminals no longer need advanced writing skills or manual research to create convincing phishing campaigns.
Real-Time Adaptation
AI systems can analyze victim responses and modify attack strategies dynamically during conversations.
Common Types of AI-Powered Phishing Attacks
Business Email Compromise (BEC)
Attackers impersonate executives or trusted employees to request payments, sensitive data, or credential access.
Credential Harvesting
Victims are directed to fake login portals designed to steal usernames and passwords.
Financial Fraud
AI-generated urgency and trust manipulation convince victims to transfer funds to attacker-controlled accounts.
Malware Delivery
Phishing emails may contain malicious attachments or links that install ransomware, spyware, or remote access tools.
Social Media Phishing
Attackers use AI-generated fake profiles and messages to manipulate victims through social platforms.
Industries Most at Risk
Financial Institutions
Banks and financial services organizations are major targets because of direct access to financial assets.
Healthcare Organizations
Medical institutions store highly valuable patient information and often face operational urgency.
Government Agencies
Governments manage critical infrastructure and sensitive national data.
Technology Companies
Tech organizations hold intellectual property, cloud systems, and privileged access credentials.
Educational Institutions
Universities often have large user populations with varying cybersecurity awareness levels.
Real-World Consequences of AI Phishing Attacks
The impact of AI-powered phishing attacks can be devastating.
Financial Losses
Organizations may lose millions through fraudulent transactions and ransomware attacks.
Data Breaches
Compromised credentials often lead to unauthorized access to sensitive systems and databases.
Operational Downtime
Cyberattacks can disrupt business operations, productivity, and service availability.
Reputation Damage
Customer trust can be severely affected after successful phishing incidents.
Legal and Compliance Risks
Organizations may face regulatory penalties for failing to protect sensitive information.
How Organizations Can Defend Against AI-Powered Phishing
Employee Cybersecurity Awareness
Security awareness training remains critical. Employees should learn to:
- Verify suspicious requests
- Identify phishing indicators
- Avoid unknown links and attachments
- Report suspicious activity immediately
Regular phishing simulations help strengthen awareness.
Multi-Factor Authentication (MFA)
MFA adds an additional layer of protection even if passwords are compromised.
Organizations should implement phishing-resistant authentication methods whenever possible.
Advanced Email Security
Modern email security solutions should include:
- AI-based threat detection
- URL analysis
- Attachment sandboxing
- Anti-spoofing technologies
- Domain authentication protocols
AI-Driven Threat Detection
Cybersecurity teams can use defensive AI tools to detect:
- Unusual login behavior
- Suspicious communication patterns
- Abnormal account activity
- Potential phishing domains
AI can significantly improve incident detection speed and accuracy.
Zero Trust Security Architecture
A Zero Trust approach assumes no user or device should automatically be trusted.
Continuous verification and least-privilege access reduce attack impact if accounts become compromised.
Incident Response Planning
Organizations must prepare for phishing-related incidents by establishing:
- Rapid response procedures
- Account isolation processes
- Communication plans
- Recovery strategies
- Security investigation workflows
Preparedness minimizes damage and recovery time.
The Future of AI-Powered Cyber Threats
AI-driven phishing attacks are expected to become even more sophisticated in the coming years.
Future threats may include:
- Real-time conversational deepfake calls
- AI-generated fake business meetings
- Hyper-personalized social engineering
- Autonomous phishing bots
- AI-generated malicious websites indistinguishable from legitimate platforms
As attackers continue evolving, organizations must adopt proactive cybersecurity strategies rather than relying solely on traditional defenses.
The battle between offensive AI and defensive AI will define the future of cybersecurity.
Conclusion
AI-powered phishing attacks represent one of the most significant cybersecurity threats of the modern digital era. By combining Artificial Intelligence with social engineering tactics, cybercriminals can create highly convincing, automated, and scalable attacks that bypass traditional defenses and exploit human trust.
From AI-generated phishing emails to deepfake voice scams and intelligent chatbots, these attacks are becoming increasingly sophisticated and difficult to detect. Businesses and individuals must understand that cybersecurity is no longer just a technical concern — it is a critical business necessity.
Organizations that invest in cybersecurity awareness, advanced threat detection, strong authentication systems, and proactive defense strategies will be far better prepared to combat the growing threat of AI-powered phishing attacks.
The future of cybersecurity depends on staying informed, vigilant, and ready to adapt against constantly evolving cyber threats.
Protect Your Business with Apprise Cyber
In today’s rapidly evolving threat landscape, proactive cybersecurity is essential for every organization. At Apprise Cyber, we help businesses strengthen their digital security posture through advanced cybersecurity solutions, security assessments, penetration testing, threat monitoring, and cyber awareness services.
Whether you are looking to secure your organization against phishing attacks, protect sensitive data, or improve your overall cybersecurity infrastructure, our expert team is here to help.
Contact Apprise Cyber Today
- Strengthen your cybersecurity defenses
- Protect your business from modern cyber threats
- Stay ahead of AI-powered attacks
- Secure your digital future with confidence
Partner with Apprise Cyber and build a safer, more resilient cybersecurity environment for your organization.