AI-Powered Cyberattacks: The New Era of Intelligent Cyber Warfare

Artificial Intelligence (AI) is transforming the digital world at an incredible speed. Businesses are using AI to automate operations, improve productivity, and strengthen cybersecurity defenses. However, cybercriminals are also taking advantage of the same technology to launch smarter, faster, and more dangerous cyberattacks.
AI-powered cyberattacks are no longer a futuristic concept — they are already reshaping the global cybersecurity landscape. From advanced phishing scams to deepfake fraud and intelligent ransomware, attackers are using AI to automate malicious activities and bypass traditional security systems.
In this article, we’ll explore how AI-powered cyberattacks work, their major types, real-world risks, and how organizations can defend themselves against this growing threat.
What Are AI-Powered Cyberattacks?
AI-powered cyberattacks are cyber threats that use Artificial Intelligence (AI) or Machine Learning (ML) technologies to automate, enhance, or accelerate different stages of a cyberattack.
Unlike traditional attacks that require continuous human involvement, AI-driven attacks can:
- Learn from data
- Adapt to security defenses
- Automate attack execution
- Analyze vulnerabilities faster
- Mimic human behavior
- Evade detection systems
These attacks allow cybercriminals to operate with greater speed, precision, and scalability than ever before.
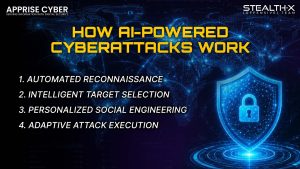
How AI-Powered Cyberattacks Work
AI-enabled attacks follow many of the same stages as traditional cyberattacks, but AI dramatically increases efficiency and sophistication.
- Automated Reconnaissance
Attackers use AI to gather massive amounts of public and private data from:
- Social media platforms
- Company websites
- Employee profiles
- Data breaches
- Online forums
AI systems quickly analyze this information to identify:
- Potential vulnerabilities
- High-value targets
- Employee behaviors
- Weak security practices
This significantly shortens the reconnaissance phase of an attack.
- Intelligent Target Selection
Machine learning models can identify individuals within an organization who are more likely to fall victim to phishing or social engineering attacks.
These may include:
- New employees
- Executives
- Finance teams
- Remote workers
- Employees with elevated system access
The attack becomes more strategic and personalized.
- Personalized Social Engineering
Generative AI tools can create highly convincing:
- Emails
- SMS messages
- Voice recordings
- Chat conversations
- Fake documents
- Social media profiles
These messages often sound human-written and contextually accurate, making them extremely difficult to detect.
- Adaptive Attack Execution
AI can continuously analyze how a victim or security system responds and automatically adjust attack behavior.
For example:
- Malware may change its signature to avoid detection
- AI bots may alter communication styles
- Attack paths may evolve based on system responses
This adaptability makes AI-driven threats significantly more dangerous.
Key Characteristics of AI-Powered Cyberattacks
Attack Automation
AI reduces the need for constant human involvement. Attackers can automate phishing campaigns, vulnerability scanning, malware deployment, and credential theft.
Faster Data Collection
AI systems process enormous datasets in seconds, allowing attackers to gather intelligence rapidly and accurately.
Hyper-Personalization
AI analyzes public data to craft highly personalized attacks that appear legitimate and trustworthy.
Real-Time Learning
AI models learn from success and failure, enabling attacks to improve continuously over time.
Advanced Employee Targeting
AI helps attackers identify employees with sensitive access or weaker cybersecurity awareness.
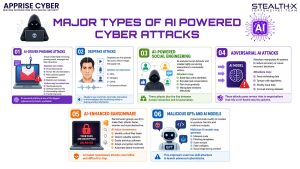
Major Types of AI-Powered Cyberattacks
AI-Driven Phishing Attacks
Traditional phishing emails often contain grammatical mistakes and suspicious wording. AI-generated phishing campaigns are much more sophisticated.
AI tools can create:
- Personalized emails
- Human-like chat interactions
- Fake customer support conversations
- Realistic scam messages
These attacks often trick victims into:
- Sharing passwords
- Clicking malicious links
- Downloading malware
- Transferring funds
AI-powered phishing is becoming one of the biggest cybersecurity threats worldwide.
Deepfake Attacks
Deepfakes use AI to generate fake audio, video, or images that appear real.
Cybercriminals can impersonate:
- CEOs
- Managers
- Clients
- Government officials
For example, attackers may create a fake voice recording instructing an employee to transfer money urgently.
Because the voice sounds authentic, victims may comply without verification.
Deepfake-based cyber fraud is rapidly increasing across businesses globally.
AI-Powered Social Engineering
AI enhances psychological manipulation by analyzing human behavior patterns and generating highly convincing communication.
Attackers may:
- Build fake online identities
- Simulate real conversations
- Gain victim trust gradually
- Manipulate emotions effectively
These attacks blur the line between human interaction and AI automation.
Adversarial AI Attacks
Adversarial AI attacks target AI systems themselves.
Attackers manipulate AI models by:
- Feeding misleading data
- Tampering with algorithms
- Modifying input data
- Corrupting training datasets
The goal is to reduce the accuracy of AI-based security systems or force incorrect decisions.
This poses serious risks for organizations heavily dependent on AI technologies.
AI-Enhanced Ransomware
Modern ransomware groups are integrating AI into their operations.
AI helps ransomware:
- Identify critical files faster
- Detect valuable systems
- Evade antivirus software
- Adapt encryption methods
- Automate lateral movement
This creates faster and more destructive ransomware attacks.
Malicious GPTs and AI Models
Cybercriminals can modify generative AI models to produce harmful outputs.
Malicious AI models may generate:
- Malware code
- Phishing templates
- Scam scripts
- Fake websites
- Social engineering content
This lowers the technical barrier for inexperienced cybercriminals.
Why AI-Powered Cyberattacks Are Dangerous
AI-powered cyberattacks introduce several serious risks:
Increased Speed
AI can launch attacks at machine speed, reducing response time for defenders.
Greater Scale
Attackers can target thousands of victims simultaneously using automation.
Better Evasion Techniques
AI malware adapts to avoid detection by traditional security tools.
Human-Like Communication
Victims struggle to differentiate between real and AI-generated interactions.
Lower Barrier to Entry
Even less-skilled attackers can use AI tools to launch sophisticated attacks.
How Organizations Can Defend Against AI-Powered Cyberattacks
Continuous Security Monitoring
Organizations should implement:
- Endpoint Detection & Response (EDR)
- Extended Detection & Response (XDR)
- Intrusion Detection Systems (IDS)
- Real-time behavioral monitoring
Continuous monitoring helps identify unusual activity before attacks escalate.
Employee Awareness Training
Human error remains one of the biggest security weaknesses.
Companies should train employees to recognize:
- AI-generated phishing emails
- Deepfake scams
- Fake customer support interactions
- Suspicious requests for credentials or payments
Regular cybersecurity awareness programs are essential.
Zero Trust Security Model
Organizations should adopt Zero Trust principles:
- Verify every access request
- Limit user privileges
- Use multi-factor authentication (MFA)
- Continuously validate identities
Zero Trust minimizes attack impact even if credentials are compromised.
AI-Powered Cybersecurity Solutions
Defenders can fight AI with AI.
Modern AI-native cybersecurity platforms use machine learning to:
- Detect anomalies
- Predict threats
- Automate incident response
- Identify behavioral indicators
- Stop attacks in real time
AI-driven defense systems are becoming essential in modern cybersecurity.
Incident Response Planning
Every organization should develop a strong incident response plan that includes:
- Threat detection procedures
- Attack containment steps
- Communication strategies
- Recovery processes
- Post-incident analysis
Fast response reduces operational and financial damage.
The Future of AI in Cybersecurity
AI is reshaping cybersecurity on both sides of the battlefield.
While cybercriminals continue developing smarter attack methods, organizations are also adopting advanced AI-powered defenses.
The future of cybersecurity will depend on:
- Faster threat intelligence
- AI-native security platforms
- Human-AI collaboration
- Real-time behavioral analysis
- Continuous adaptation
Businesses that fail to evolve their cybersecurity strategies may struggle against next-generation AI threats.
Final Thoughts
AI-powered cyberattacks represent a major evolution in cyber warfare. These attacks are faster, smarter, more scalable, and significantly harder to detect than traditional cyber threats.
From deepfake scams and AI phishing to intelligent ransomware and adversarial AI, organizations now face a threat landscape that is constantly evolving.
The solution is not to fear AI — but to secure against its misuse through modern cybersecurity practices, employee awareness, and AI-native defense technologies.
Secure Your Business with Apprise Cyber
At Apprise Cyber, we help businesses stay protected against modern cyber threats, including AI-powered attacks, ransomware, phishing, and advanced social engineering campaigns.
Our cybersecurity solutions are designed to help organizations:
- Detect threats faster
- Protect sensitive data
- Secure cloud environments
- Prevent cyberattacks
- Strengthen digital infrastructure
- Improve incident response capabilities
Whether you are a startup, enterprise, or growing business, Apprise Cyber provides professional cybersecurity services tailored to your security needs.
AI-powered cyber threats are evolving every day — is your business prepared?cyber
Contact Apprise Cyber today and strengthen your cybersecurity defenses before attackers strike.
Protect your systems. Secure your data. Defend your future.