A Wake-Up Call for Digital Trust and Cybersecurity
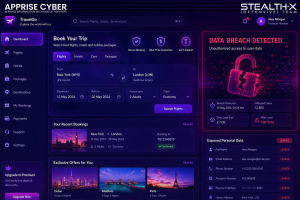
In today’s rapidly evolving digital landscape, convenience often comes at the cost of security. One of the latest incidents highlighting this risk is the Booking.com data breach, which has raised serious concerns about user data protection, third-party risk management, and customer trust.
This incident serves as a critical reminder for both organizations and users to rethink cybersecurity practices in an interconnected ecosystem.
Overview of the Incident
Booking.com, one of the world’s leading online travel platforms, recently faced a data security incident where unauthorized third parties gained access to customer reservation data. While the company stated that financial information was not compromised, the breach exposed personally identifiable information (PII), including:
- Customer names
- Email addresses
- Phone numbers
- Booking details
- Addresses
- Additional information shared with hotels
Such data, even without financial details, is highly valuable for cybercriminals, especially in launching targeted phishing and social engineering attacks.
User Experiences and Rising Concerns
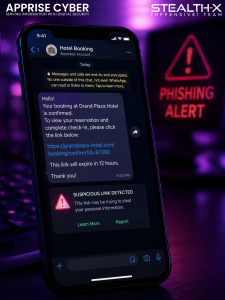
Several users reported alarming experiences after making reservations through the platform. Victims received highly personalized scam messages, often via WhatsApp, referencing their exact booking details.
One such user shared that they were asked to click a malicious link to “secure” or “cancel” their reservation. Fortunately, they identified it as a scam. However, the disturbing part was that the attackers already had access to sensitive booking information.
This clearly indicates that:
- Attackers leveraged real user data to gain trust
- Scams were highly targeted, not random
- The breach had real-world implications beyond just data exposure
Customer Support and Communication Gaps
A major concern highlighted by users was the lack of timely and effective response from Booking.com’s customer support.
Many users reported that:
- Complaints were not addressed promptly
- The issue was often shifted to third-party hotels
- There was no clear accountability or transparency
This reflects a critical failure in incident response management, where organizations must not only contain breaches but also communicate effectively with affected users.
Official Response from Booking.com
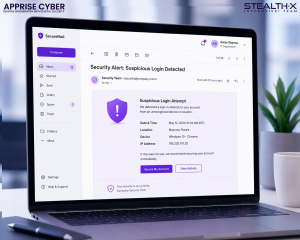
Following multiple reports, Booking.com issued an email notification acknowledging suspicious activity. The company stated that:
- Certain reservation data had been accessed
- Booking PINs were reset as a precaution
- Users should remain alert for phishing attempts
While these steps indicate a reactive approach, they also highlight the need for proactive cybersecurity measures.
Regulatory and Compliance Implications
Another significant aspect of this incident was the delay in reporting the breach. Booking.com reportedly informed the Dutch privacy regulator 22 days late, resulting in a fine of €475,000.
This raises serious concerns regarding:
- Compliance with data protection regulations
- Timely breach disclosure
- Organizational transparency
In regulated environments, delayed reporting can damage not only reputation but also legal standing.
Cybersecurity Analysis: What Went Wrong?
From a cybersecurity perspective, this breach exposes several weaknesses:
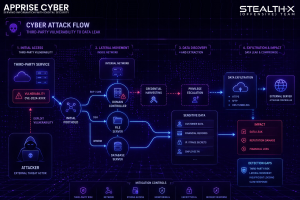
- Third-Party Risk Exposure
Booking platforms rely heavily on hotels and partners. Weak security controls at any point in the chain can lead to data leakage.
- Inadequate Data Protection
Even non-financial data, if not properly secured, can be weaponized for phishing and identity-based attacks.
- Lack of Proactive Monitoring
Delayed detection and response suggest gaps in threat monitoring and incident detection systems.
- Poor User Communication Strategy
Failure to inform users promptly increases the risk of further exploitation.
Lessons for Organizations
This incident provides valuable insights for businesses handling customer data:
- Implement Zero Trust Architecture to minimize unauthorized access
- Strengthen Third-Party Security Assessments before data sharing
- Adopt Real-Time Threat Detection Systems
- Ensure Transparent Incident Communication Plans
- Regularly conduct penetration testing and security audits
How Users Can Protect Themselves
While organizations bear primary responsibility, users should also adopt safe practices:
- Avoid clicking on suspicious links, even if they seem legitimate
- Verify communications through official platforms
- Use antivirus and endpoint security tools
- Enable multi-factor authentication (MFA) wherever possible
- Monitor bookings and accounts for unusual activity
Conclusion
The Booking.com data breach is more than just a security incident—it is a wake-up call for the entire digital ecosystem. It demonstrates how even limited data exposure can lead to serious consequences when exploited intelligently.
For cybersecurity professionals and organizations, this case emphasizes the importance of data protection, rapid response, and accountability.
At Apprise Cyber, we believe that cybersecurity is not just about defense—it’s about building trust, resilience, and proactive protection strategies in an increasingly connected world.